Reserve Bank of India (RBI) cybersecurity compliance often feels confusing from the very beginning.
The requirements are extensive, the language is deliberately flexible, and there is no single checklist that guarantees success during an audit. At the same time, the consequences of gaps are significant, ranging from financial penalties to operational restrictions and reputational damage.
This raises a practical question for most organizations: how to approach RBI requirements in a way that is structured, realistic, and sustainable over time.
What RBI cybersecurity compliance actually involves
Over the years, the Reserve Bank of India has issued hundreds if not thousands of requirements in various areas through circulars and regulatory acts. Since 2016, these have been consolidated into Master Directions, each covering a specific domain.
For cybersecurity, the key document today is the Master Direction on Information Technology Governance, Risk, Controls and Assurance Practices (2023). It replaced earlier circulars and now serves as the primary reference point for IT and security obligations.
This direction applies to a wide range of regulated entities, including
- commercial banks,
- small finance banks,
- payment banks,
- Non-Banking Financial Companies (NBFCs) (with some exceptions),
- Credit Information Companies, and national financial institutions such as the National Bank for Agriculture and Rural Development (NABARD)
- the Export-Import Bank of India (EXIM Bank).
Foreign banks operate under the “comply or explain” model, where deviations are possible if justified and approved.
In practice, organizations operating in the Indian financial sector are expected to align their cybersecurity processes with this framework.
Why RBI audits are harder than they look
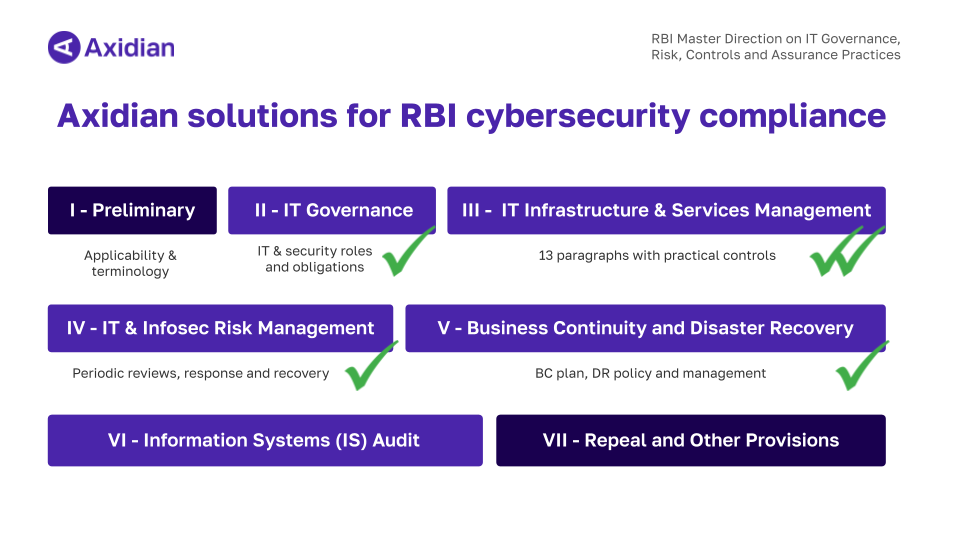
At first glance, the Master Direction may seem manageable, with a relatively small number of high-level requirements. It consists of seven chapters that cover governance, infrastructure, risk management, business continuity, and audit processes.
The difficulty comes from interpretation and application.
Many requirements use flexible language such as “appropriately secured” or “adequately controlled.” These definitions may be intentionally open-ended to tailor the audit committee’s approach to each regulated entity individually, based on its size, infrastructure complexity, and risk exposure.
In other words, audits are risk-based and adaptive. Auditors evaluate:
- previous findings
- how identified gaps were remediated
- whether improvements are consistent over time
As a result, RBI cybersecurity compliance cannot be reduced to a fixed list of controls. Without clear guidance, preparation often becomes reactive and fragmented.
A practical way to approach RBI compliance
Working directly with the full set of RBI requirements can quickly become overwhelming. The document is comprehensive, but it is not structured as an implementation roadmap.
To make this manageable, Axidian developed a practical compliance guide with structured checklists based on the Master Direction. This document translates regulatory expectations into a format that is easier to work with in real-life scenarios. Let’s take a closer look at how this approach is structured.
Breaking down the Axidian RBI compliance guide
The controls in the RBI Master Direction can be grouped into three core areas:
- documentation
- technology controls
- recurring activities
This structure reflects how compliance is implemented in real environments. It helps teams break down regulatory requirements into actionable tasks, prioritize efforts, and track progress throughout the audit preparation process.
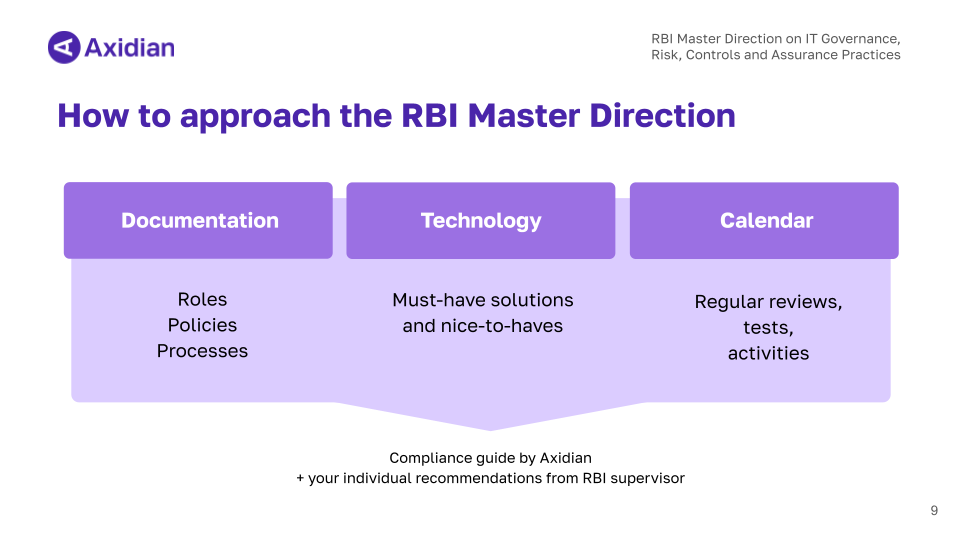
Documentation: building auditable structure
The documentation checklist developed by Axidian includes all materials that are either explicitly required or implicitly expected by RBI.
During our analysis of the Master Direction, we identified multiple references to documentation requirements across different chapters — from governance frameworks to incident response procedures. While RBI does not provide a single consolidated list, the expectation is clear: key processes, roles, and decisions must be formally documented.
A more effective approach is to build a structured documentation inventory where each document is tracked with:
- its current status
- the responsible owner
- the date of the last update and approval
- a direct link to the document
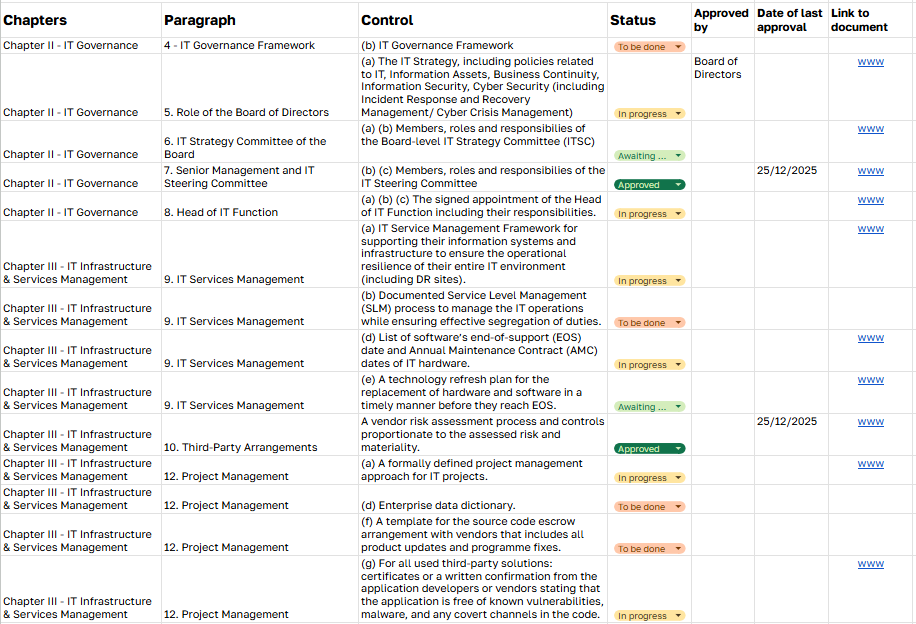
This level of organization makes a significant difference during audits. Instead of searching for scattered files or relying on explanations, teams can quickly demonstrate that required controls are defined, maintained, and regularly reviewed.
Well-structured documentation not only improves audit readiness but also creates clarity in day-to-day operations and governance.
Technology controls: implementing required safeguards
The technology checklist developed by Axidian outlines the types of software that are either explicitly required or implicitly expected by RBI.
It includes two categories.
First, there are solutions you cannot realistically operate without if you want to meet RBI requirements. These include, for example, multi-factor authentication (MFA) and privileged access management (PAM), which are directly referenced in the Master Direction.
Second, there are supporting tools that are not explicitly mandated but significantly simplify compliance efforts. A typical example is a Governance, Risk, and Compliance (GRC) platform, which helps organize policies, track controls, and manage audit readiness more efficiently.
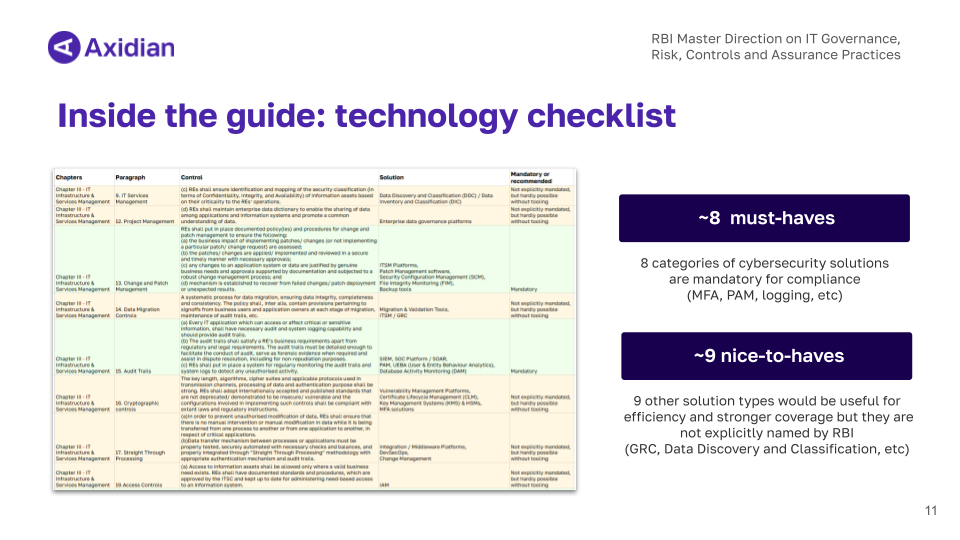
Importantly, this technology checklist is vendor-agnostic. It does not prescribe specific products or providers. Instead, it defines the types of solutions you should evaluate based on your environment and requirements.
At the same time, not every organization will require the full set of tools listed. The final selection depends on:
- the maturity of your processes
- the size of your team
- how much you choose to automate versus manage manually
The checklist is intended as a reference point. You can use it as is, adapt it to your environment, or build your own based on the same structure.
Cybersecurity calendar: ensuring consistency over time
The third part of Axidian’s approach is the calendar checklist, which brings together all activities from the Master Direction that must be performed on a recurring basis.
This includes:
- regular reviews and assessments
- vulnerability scans and penetration testing
- audit-related activities
- governance and reporting processes
Each of these actions needs to be structured and tracked over time.
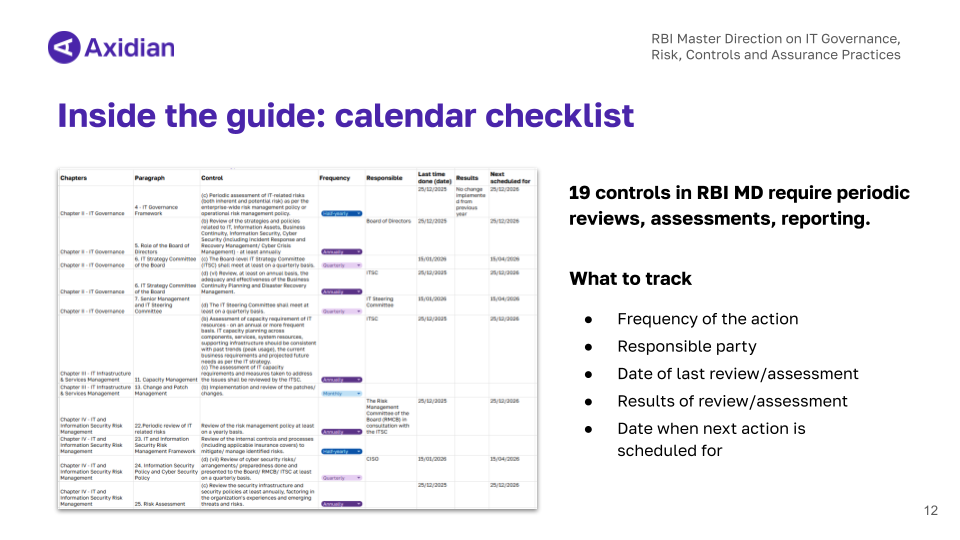
In practice, this means defining for every activity:
- its frequency
- the responsible owner
- the date of the last execution
- the outcome
- the next scheduled review
This approach helps ensure that compliance-related tasks are not performed sporadically, but become part of a consistent operational cycle.
A useful way to think about this is through a simple analogy. After a medical appointment, the doctor recommends the time of next visit and many prefer to book it immediately. Cybersecurity processes benefit from the same discipline. Once a recurring activity is completed, the next date should already be defined and recorded.
This creates continuity and reduces the risk of missed controls.
How to prepare for an RBI audit step by step
The structure described above — documentation, technology, and calendar — reflects how Axidian approaches RBI cybersecurity compliance.
At the same time, RBI audits remain context-dependent. Supervisors may focus more closely on specific areas depending on the organization’s risk profile, past findings, and operational complexity.
This means that no checklist can fully replace judgment.
However, a structured framework provides a strong starting point — not only for achieving compliance, but also for maintaining a consistent and manageable cybersecurity process beyond regulatory requirements.
Here’s a step-by-step guide on how to use the provided checklist.
- Assigning responsibility: a compliance team or a person who’ll coordinate audit preparation.
- Gap analysis — comparing current practices with RBI requirements to identify missing elements across policies, processes, and technology.
- Once gaps are identified, organizations move to implementation. This includes introducing new controls, updating existing processes, and aligning systems with regulatory expectations.
- Documentation: all implemented controls must be recorded and supported with evidence such as logs, reports, and formal documents.
- Finally, recurring activities are mapped into a cybersecurity calendar, ensuring that reviews, testing, and governance processes are carried out consistently.
Where most RBI audit findings occur
In practice, access control is one of the most common sources of audit findings.
RBI emphasizes the principle of need-based access, meaning users should only have access to resources required for their role.
This applies particularly to privileged accounts, where risks are higher.
RBI requires organizations to:
- limit and regularly review access rights
- monitor privileged activity
- maintain logs and conduct periodic reviews
- enforce MFA for critical access
Managing these requirements manually is difficult at scale.
Axidian Privilege enables centralized control of privileged access, including credential management, session monitoring, and enforcement of the Least Privilege principle.
Axidian Access provides a unified access point to corporate resources for regular users through flexible authentication mechanisms.
Together, these controls help establish consistent and auditable access practices.
What changes with a structured approach
Organizations that adopt a structured compliance model move away from reactive audit preparation and gain a much clearer operational footing.
They achieve:
- visibility into access and user activity
- predictable processes for reviews and audits
- documented evidence readily available for inspection
In projects with Indian banks, this approach has consistently resulted in faster audit preparation, fewer critical findings, and stronger coordination between IT and compliance teams.
For a deeper look at how this works in practice and a detailed walkthrough of RBI cybersecurity compliance — you can explore the Axidian webinar. Olesya Druzhinina, Head of Business Development, and Kirill Bondarenko, Regional Sales Director, explain how organizations structure their compliance efforts and apply the checklists discussed in this article.
Watch the webinar and download the compliance guide to start building your own approach.