A single remote access point
In terms of architecture, the PAM system is a dedicated group of servers, to which remote users
need to connect if they want to work with target resources. The PAM connection interfaces can be
located in the demilitarized zone (DMZ) of your corporate network, while the administrator
interface can be hosted in a different segment of your network.
Unlike with network hardware, firewalls, and a next generation firewall (NGFW), in this case, the
user will initially connect to the PAM system servers and only then to the target resource. This
connection protocol will allow you to introduce additional measures to enable remote desktop user
activity monitoring and event recording. Furthermore, in order to subsequently connect to the
target resource, a user must be expressly logged into the PAM system and have access rights to a
certain restricted list of resources.
The PAM system will be handled by an information security administrator rather than a network
administrator, which will rule out the possibility of assigning unauthorized remote access rights
by an employee who doesn’t have appropriate permissions.
Users will be connected via the RDP or SSH protocols, which will ensure maximum limitations on
the network traffic in case of external access to the PAM system.
In light of the above, the PAM platform can be utilized not only when your company has a plan to
transition to remote work, but also when you need to urgently deploy temporary remote access,
including granting access to non-privileged users.
Two-factor authentication
The Axidian Privilege platform supports out-of-the-box 2FA with one-time passwords delivered to the
user’s phone. This will help mitigate the threat of password theft for your employees with
authorized remote access privileges.
Even if a password is stolen, the intruder will not be able to connect to the target resource
without having the actual phone to which one-time passwords are sent. If the phone was lost, your
employee will definitely notice this and notify the security administrators. After that, one-time
passwords can be sent to another device.
2FA has an added advantage − it can also be used against internal malicious users (insiders). In
case of remote connection, such users may steal information or disrupt the operation of one of the
company’s services and then claim that their passwords were stolen and they are «victims»
themselves, once the breach has been uncovered. If the two-factor authentication is used, such
users can no longer say that they had nothing to do with recorded malicious activity. Insiders
will have to admit that they are responsible for a security breach, or it occurred with their
tacit consent if their phone was stolen and they failed to inform a security administrator in a
timely manner.
Access management policy
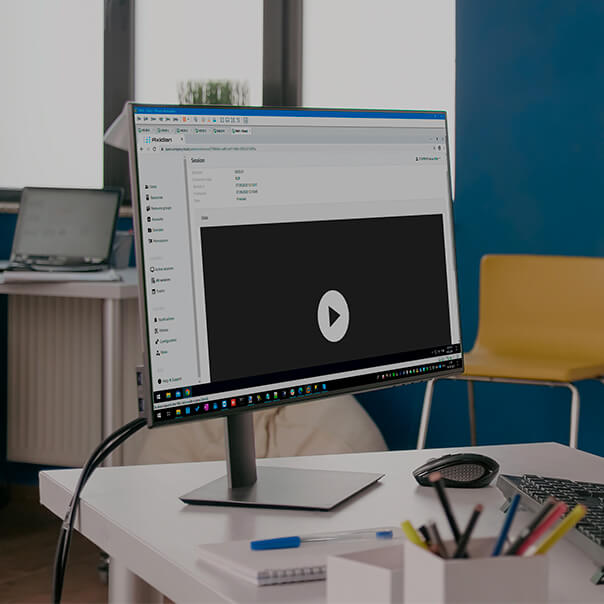
Axidian Privilege relies on overarching access management policies, which eliminates the need for
additional setup of various network equipment and target resources. It will enable you to use a
single console for assigning access rights to almost any available target resource for any
privileged user.
In addition to direct setup of «user-to-resource» access, access management policies will allow
you to configure:
- Access protocol, or target application
- Allowed access time
- Required approval before connection
- Session monitoring and recording parameters
- Privileged accounts available for connection
- Etc.
All these settings are incorporated in one and the same solution and are available in a single
console, which sets the Axidian Privilege system apart from other available access management technology.
Scheduled and temporary access
The Axidian Privilege software suite will allow you to schedule access to target servers and
applications (for example, from 9am to 6pm), as well as assign temporary access rights (valid up
until a certain date).
Similar access rules are available in network hardware (rules for filtering traffic by time
periods), but they do not permit the use of other access management mechanisms and are often
limited to actions (traffic is filtered at the node-to-node level).
You can use the PAM system to set up scheduled access and temporary access based on the
«user-to-server» or «user-to-resource» rules. The list of target resources includes not only
servers but also applications.
You can also opt to integrate the PAM system with the Service Desk (request processing system)
via API, thereby enabling the automatic generation of scheduled access rules.
Access upon approval
Axidian Privilege supports the option of required prior access approval by the administrator or resource
owner.
If you use network equipment, this access option can only be introduced manually, and you will
also need to engage additional specialists. And in this case, no one can guarantee that the new
«temporary» rules will be withdrawn when they are no longer needed.
You can use this option if a privileged user urgently needs to connect to a critical resource
beyond standard business hours (for example, in the event of failure). If the PAM system is used,
your employee will just need to specify the reason why they need to connect to your corporate
infrastructure, which will be recorded in the event log.
Another situation concerns gaining access to a critical resource at any time, but only after
obtaining explicit approval of the authorized personnel. All works should be carried out on the
basis of relevant requests. However, it may be hard to establish a connection schedule (for
example, if the connection is possible only when the server load is low, while the actual server
load is a dynamic value).
Access via specialized protocols
You can use the Axidian Privilege access servers to configure access settings for target servers via
various remote access and administration protocols.
The out-of-the-box Axidian Privilege solution supports the following most common remote access
protocols:
- RDP (Remote Desktop Protocol)
- SSH (text console)
- HTTP (web interface)
If you need to use a specialized proprietary protocol, you can publish a relevant application
(thin client) on the built-in terminal server, connect to this app, and then use it for your
subsequent operations on the target resource. It is worth mentioning that you will have an option
to publish outdated and custom applications. This means that the system is designed to support
even rare proprietary protocols, which otherwise may be close to impossible.
The Axidian Privilege functionality enables controlled and secure remote access to almost all categories
of target resources for all categories of users.
Terminal access to applications
As one of its components, Axidian Privilege includes a dedicated access server based on the Microsoft
RDS terminal server.
Thanks to this terminal server, the system not only supports additional proprietary and rare
remote protocols but also allows direct publication of corporate applications.
This functionality may be useful when you require remote access to critical applications that are
not related to the administration and management of IT components (financial applications,
electronic document management system, etc.). In particular, Axidian Privilege will allow you to set up
access schedules for such apps or request prior access approval on behalf of an administrator or
another official.
Minimal user privileges
If you use the Axidian Privilege platform to set up controlled and secure remote access to your
corporate resources, in many cases it may be sufficient to grant access rights only for a specific
application, rather than an entire workstation or server. This way you can make sure that your
users have minimal privileges, thereby reducing the risk of their erroneous and destructive
activity on the target server.
The same is true for temporary access, scheduled access or access upon approval, and command
input control. At your discretion, these rules can apply only to remote work, while your personnel
will retain all privileges when they come to work on the company premises.
By using the Axidian Privilege functionality, you can significantly reduce the number of cases when you
need to edit user privileges in a domain or corporate app. This, in turn, can help you save time
and minimize the risk of errors when making adjustments in permissions.