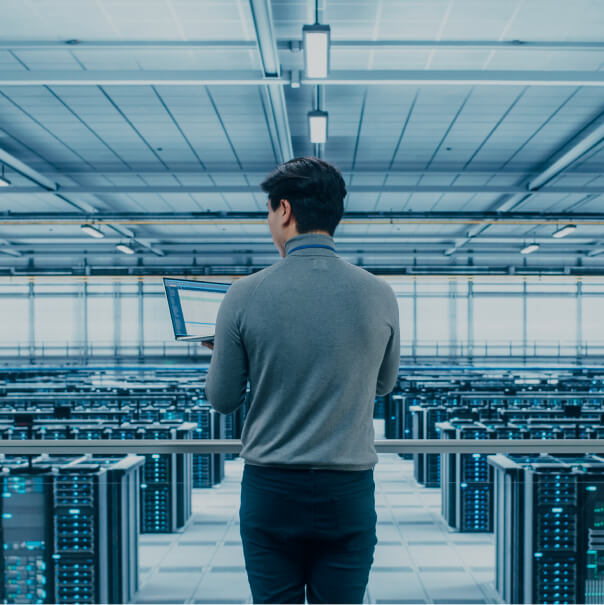
In finance, actual funds are the core asset. Funds can be earmarked for addressing various tasks, including corporate development. A major part of operations in financial institutions is related to bank transactions, and modern IT and automation tools are widely used for such tasks. Finance is rightfully considered one of the most automated economic sectors.
In the modern world, it is safe to say that money is yet another type of information. At its core, money is information about financial resources owned by legal entities or individuals. It is becoming increasingly easy to manage digital money in your bank account, do cashless shopping, and send funds to other accounts, and we can safely store substantial amounts in the bank. This means that over time, cash use is likely to continue downscaling.
Financial institutions, especially those operating in the banking sector, place a major focus on information security issues. In no small part this has to do with the fact that unauthorized access to financial resources enables attackers to steal funds almost immediately (which is not true for sectors focusing on other resources, for example, manufacturing or public sector).
This is why despite top security levels, the financial sector remains one of the main targets of cyberattacks. Criminals mainly target financial systems where they can make quick profits.