There is no stopping progress, and the market keeps coming up with more advanced IT solutions: new versions of operating systems, application software with enhanced functionality, and innovative hardware products.
Yet, most companies remain loyal to outdated software and do not even plan to migrate to new solutions. They may do so for a number of reasons — they may find it hard to give up on their habits or consider the new systems too sophisticated, hard to use, or inefficient.
While usability and efficiency of old vs. new products is a matter of debate (since these categories are largely subjective), information security is a factor that cannot be treated lightly. What is meant here is not just embedded security functions of a given software product, but its overall resilience to cyber attacks.
Unfortunately, it is hardly possible to develop an IT solution without a single vulnerability: a new vulnerability is bound to be discovered sooner or later, and it can only be eliminated by the developer who should promptly release a relevant update.
Integration with new software and hardware may prove even more challenging. It’s hard to believe that anyone would want to face an unsolvable task and one day discover that their new software is not compatible with their outdated products, and the developer no longer offers technical support or updates.
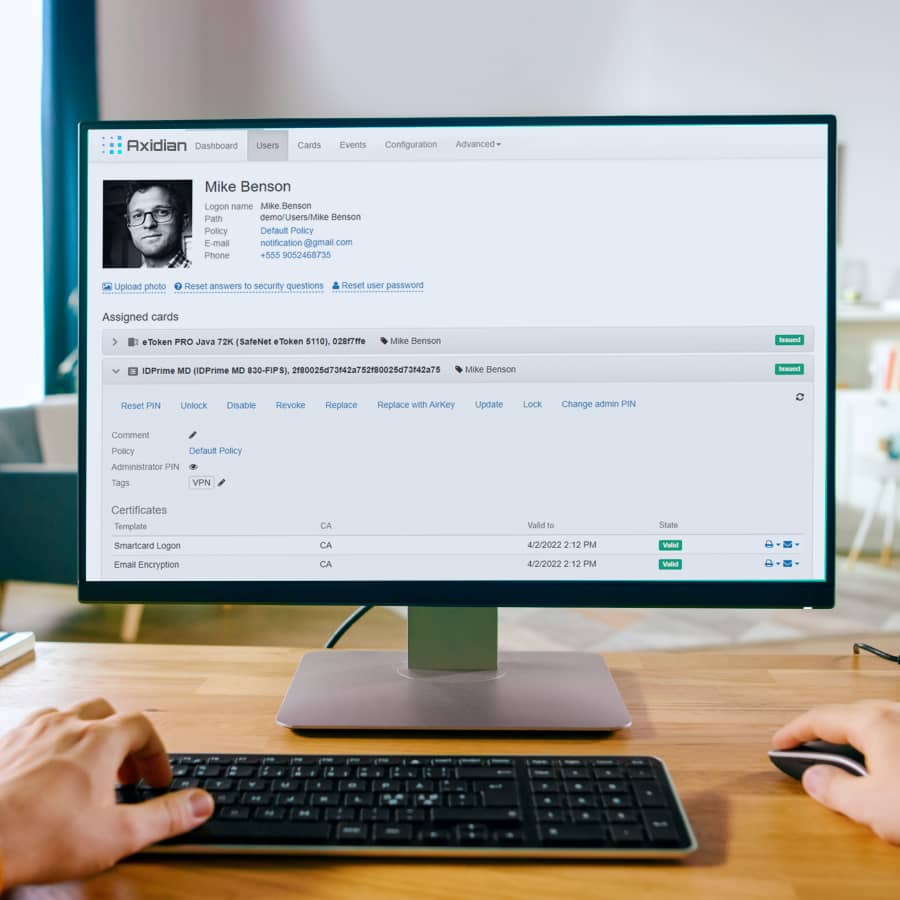
Even today, most companies continue to use SafeNet Authentication Manager (SAM) for managing their public key infrastructure, disregarding the fact that this system is severely outdated and no longer supported.
On top of glaring cyber security threats, abandonware in PKI management is bound to face a number of limitations in the future. New models of smart cards will be released, new algorithms introduced, new third-party software and operating systems deployed — and in the end, your out-of-date software will no longer be able to support new technology.
If you want to avoid this situation, your best choice would be to migrate to a different PKI Management product that is being supported and regularly updated by the developer.