The Saudi Arabian Monetary Authority (SAMA) issued its Cyber Security Framework (CSF) to enable Financial Institutions to effectively identify and address risks related to cyber security. This initiative aims to ensure confidence in the Saudi financial sector.
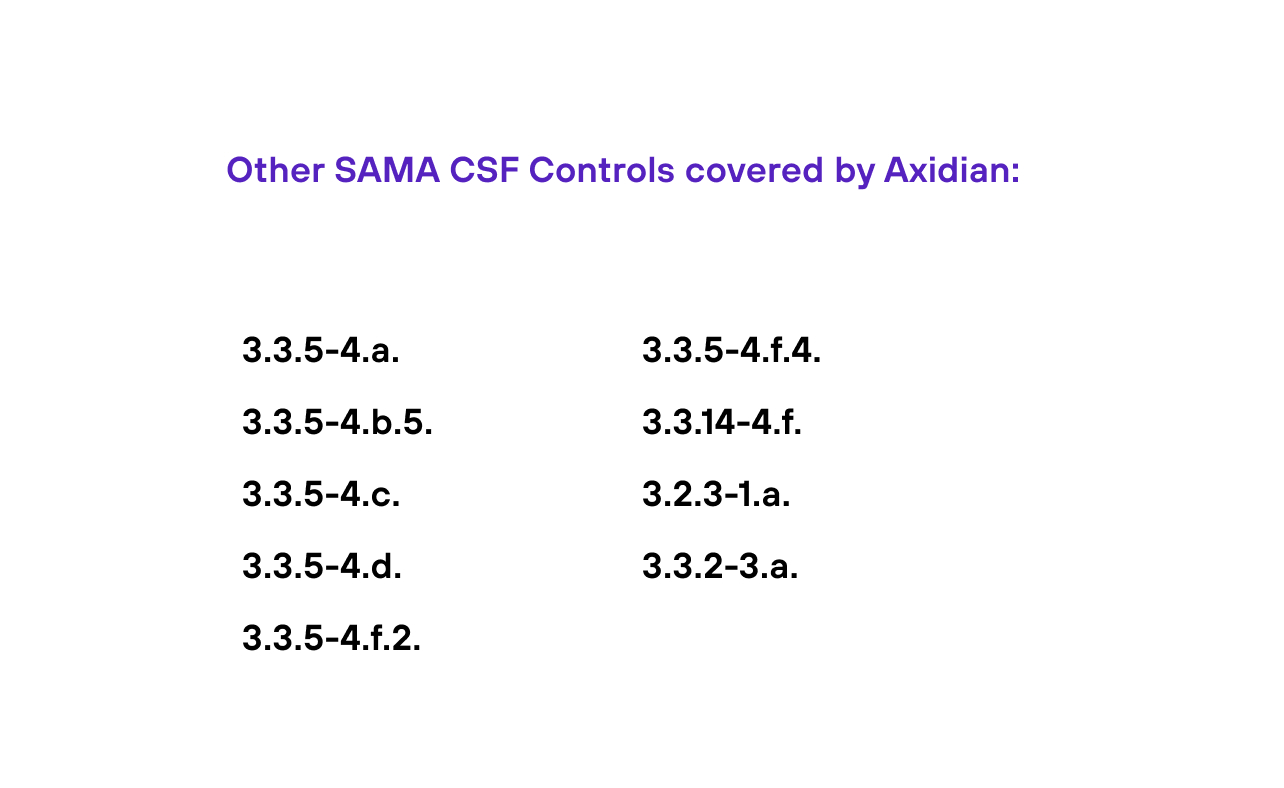
The Framework consists of 249 controls across 4 cybersecurity domains:
- Cyber Security Leadership and Governance
- Cyber Security Risk Management and Compliance
- Cyber Security Operations and Technology
- Third Party Cyber Security
These cybersecurity controls are linked to related national and international law and regulatory requirements.