More than 1,000 password attacks happen every second, and over 99.9% of compromised accounts didn’t have MFA enabled, according to Microsoft.
For most organizations, Multi-factor authentication(MFA) is already part of the roadmap. The more difficult decision is how to choose MFA in a way that genuinely reduces exposure rather than simply adding another login step.
Hardware tokens, one-time passwords, push notifications, biometrics — every method claims to improve security. But selecting the right option is rarely about technology alone. To choose MFA effectively, organizations need to look at how users work, what systems they access, and which risks truly matter.
This article explains what MFA is, why it matters, and how to choose MFA in a way that fits real business environments in MENA.
What MFA really is and what it is not
Multi-factor authentication verifies identity using more than one category of factor: something a user knows, something they have, something they are, or contextual signals such as location or device. In practice, MFA reduces the impact of stolen credentials by ensuring that a single compromised element is not enough to gain access.
What MFA does not do is magically fix weak access design. If authentication methods are chosen without understanding how people work, MFA becomes friction — and friction always finds a workaround.
This is where many implementations quietly fail.
Why there is no “best” MFA method
When organizations choose MFA, decisions often assume that stronger technology automatically means better security. In reality, security outcomes depend on fit, not strength. The effectiveness of MFA is defined less by how advanced a method appears and more by how well it aligns with real access scenarios.
An MFA method that works perfectly for remote VPN access may be unrealistic for administrators managing systems all day. A method suitable for office employees may break down when applied to contractors, healthcare staff, or industrial operators. The same organization may need different assurance levels for email, internal systems, and privileged access and no single method can serve all of them equally well.
In MENA, this complexity is amplified. Organizations frequently operate across multiple locations, with a mix of on-prem systems, legacy applications, and cloud services.
Compliance frameworks often define minimum controls, but those controls rarely map one-to-one to real access risks. As a result, MFA needs to adapt to context rather than simply satisfy a requirement.
SMS and email OTP: where simplicity helps and where it quietly breaks
SMS and email-based one-time passwords are often the first MFA method organizations deploy. They are easy to understand, require almost no onboarding, and work across a wide user base. This makes them appealing for public-facing services, temporary access, or early-stage MFA rollouts.
In practice, many government portals and large enterprises still rely on SMS OTP for low-risk access, simply because it matches the reality of their user population. When you have thousands of users with different devices and technical maturity, SMS feels like the least disruptive option.
The convenience of SMS OTP hides structural weaknesses. SMS relies entirely on mobile networks and telecom processes that sit outside the organization’s control. SIM swap attacks, SS7 interception, and delayed message delivery are not rare edge cases — they are well-documented risks. In environments where privileged or sensitive systems are involved, this dependency becomes difficult to justify.
Email-based OTP is slightly more resilient in comparison, as it does not depend on telecom infrastructure. However, it introduces its own exposure. If the user’s mailbox is compromised, the attacker can intercept both the password reset and the second factor in the same channel. In cases where email itself is the protected resource, using email OTP creates circular protection — the factor is delivered to the very system it is supposed to defend.
For that reason, both SMS and email OTP can be acceptable for low-risk scenarios, but neither should be considered strong protection for sensitive or administrative access.
TOTP apps: a practical step forward, with trade-offs
Time-based one-time password apps are often the next step for organizations that want stronger assurance without excessive complexity. They remove reliance on telecom infrastructure and are widely supported across enterprise systems.
TOTP apps are commonly used for VPN access, internal applications, and day-to-day employee authentication. They strike a workable balance between security and usability, especially in hybrid environments where users move between office and remote work.
However, TOTP is still vulnerable to phishing and real-time credential capture. If a user enters a valid code into a fake interface, the system cannot tell the difference. Operationally, TOTP also introduces challenges around device loss, backup, and recovery — problems that only surface after rollout, not during planning.
TOTP improves security posture, but it does not eliminate the need for access policies and monitoring.
Push authentication: usability at scale and its hidden risks
Push-based MFA is popular because it feels effortless. Users receive a notification, tap “approve,” and move on. For organizations with frequent logins and web-based systems, this dramatically reduces friction.
Many enterprises adopt push authentication for internal platforms and shared services, especially where productivity concerns dominate. In environments with mobile-first users, push can feel like the most natural option available.
The downside emerges over time. Repeated push prompts condition users to approve requests reflexively, creating exposure to MFA fatigue attacks. Without safeguards such as number matching, contextual information, or risk-based limits, push authentication can quietly degrade into a weak control — even though it appears modern and user-friendly.
Push works best when treated as part of a broader policy framework, not as a standalone solution.
Hardware tokens and security keys: where assurance matters most
Hardware tokens and cryptographic security keys are often associated with high-security environments and for good reason. They provide strong resistance to remote attacks and are well suited for scenarios where access misuse would have serious consequences.
In sectors such as government, finance, and critical infrastructure, hardware-based MFA is frequently used for privileged accounts and administrative access. The number of users is usually limited, the risk is clear, and the operational overhead is justified.
That said, hardware tokens introduce their own realities: distribution, replacement, lifecycle management, and user training. They are rarely practical for broad user populations, but they are extremely effective when applied selectively — especially in PAM scenarios.
Biometrics: fast, familiar, and rarely sufficient alone
Biometric authentication is increasingly common on managed devices, particularly in healthcare and corporate workstation environments. Fingerprint or facial recognition reduces friction for frequent access and can significantly improve user acceptance.
However, biometrics should not be treated as a standalone factor. They are device-bound, rely on local security, and cannot be changed if compromised. In practice, biometrics work best when combined with possession-based factors, forming a layered approach rather than a single gate.
Where MFA implementations usually go wrong
Most MFA failures are not caused by weak technology, but by weak design decisions. Organizations often deploy one method everywhere because it is easier to manage, only to discover that it fits nowhere particularly well. Others add MFA without central policies, leaving each system to enforce controls differently.
Another common issue is treating MFA as a static project. Access patterns change, systems evolve, and user behavior adapts — but MFA configurations remain frozen. Over time, the gap between policy and reality grows, and controls lose effectiveness.
How to approach MFA selection in practice
Choosing a sustainable MFA strategy starts with understanding access, not tools. Organizations that succeed take the time to choose MFA based on a clear view of who accesses what, from where, and under which conditions. From there, authentication methods are aligned with actual risk levels rather than user convenience alone.
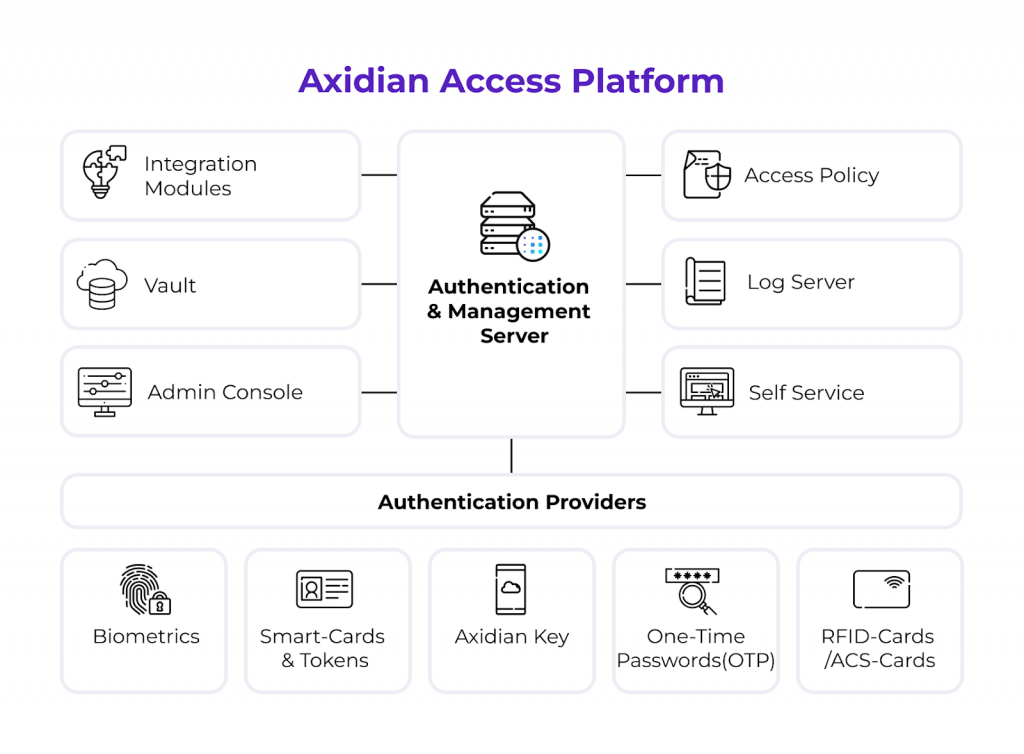
Centralized policy enforcement becomes critical at this stage. MFA should be consistent in logic, even when methods differ. This is why platforms like Axidian Access are used in practice — not to promote a single authentication method, but to apply different MFA approaches across VPNs, desktops, cloud apps, and internal systems through unified policies.
Testing and adjustment are equally important. Short pilot phases often reveal usability issues, unexpected workflows, or integration gaps that no architecture diagram can predict.
MFA only works when it fits real access behavior
MFA is not a product choice — it is an access design decision. Its effectiveness depends less on how strong a method looks on paper and more on how well it aligns with the way people actually work across different systems and roles.
When MFA respects context, users accept it. When it ignores reality, it gets bypassed.
This is why mature MFA strategies rely on flexibility rather than a single “best” method. Organizations need the ability to apply different authentication factors to different access scenarios — from VPNs and business applications to desktops and privileged systems — while keeping policies consistent and manageable.
That’s the role platforms like Axidian Access play in practice. Instead of forcing one MFA method everywhere, Axidian Access allows organizations to combine multiple authentication methods, integrate them with existing infrastructure, and enforce access policies centrally — adapting MFA to real workflows rather than redesigning workflows around MFA.
The most important decision is not which MFA method to choose, but where and why to apply each one.