RBI compliance often looks clear on paper — until you try to implement it. Requirements are broad, expectations depend on context, and there is no single checklist that tells you what to do step by step.
In our previous article, we explained how to approach RBI cybersecurity compliance using a structured framework and practical checklists. If you haven’t read it yet, start here.
Now let’s move one step further — from understanding the requirements to actually implementing them.
From RBI requirements to real implementation
Knowing what RBI expects is only half of the work. The harder part is turning those expectations into real controls, processes, and tools that auditors can verify.
RBI compliance is not about documentation alone. It requires enforceable controls — access must be restricted, activities must be monitored, and risks must be managed continuously. Without the right technologies in place, even well-prepared documentation will not hold during an audit.
This is where implementation becomes critical. Let’s look at how Axidian solutions help translate RBI requirements into practical, auditable controls.
Why MFA and PAM are mandatory for RBI compliance
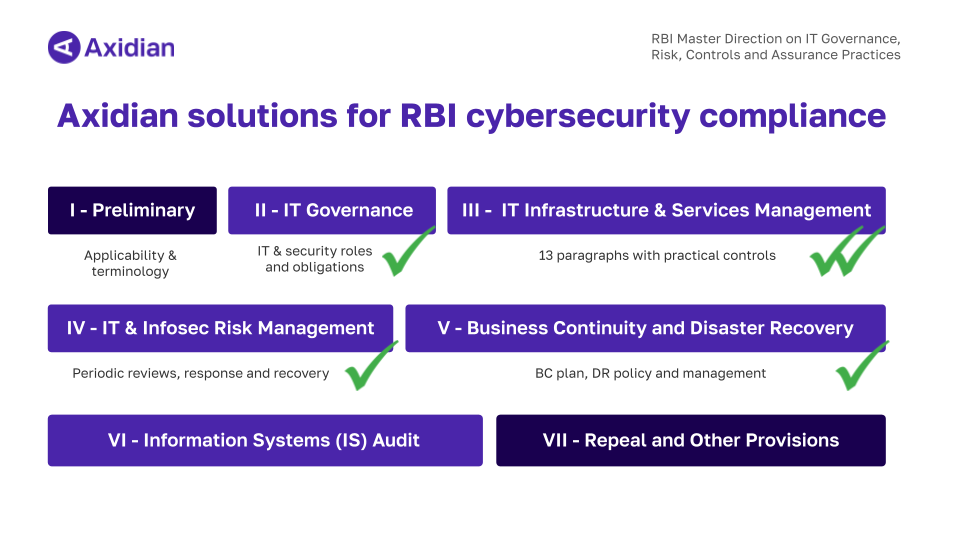
Some RBI requirements are not open to interpretation. In Chapter 4 of the Master Direction on Information Technology Governance, Risk, Controls and Assurance Practices, controls explicitly require:
- Multi-factor authentication (MFA)
- Privileged access management (PAM)
These are not “recommended” measures — they are mandatory. Without them, organizations cannot meet core RBI compliance guidelines.
MFA ensures that access to critical systems is protected beyond passwords. PAM ensures that privileged users — administrators, engineers, third parties — are controlled, monitored, and auditable.
Together, these controls form the foundation of any RBI compliance checklist for banks and NBFCs.
Access control and least privilege: how to meet RBI control #19
Need-based access: what RBI expects
RBI Control #19 (a) states that access to information assets should only be granted where there is a valid business need. In practice, this translates into the principle of least privilege — users should only have access to what they actually need to perform their tasks.
This sounds straightforward, but in real environments, access tends to accumulate. Users change roles, projects evolve, and permissions are rarely reviewed systematically. Over time, this leads to excessive access — one of the most common audit findings.
How Axidian Privilege helps control privileged access
Axidian Privilege (PAM) helps enforce least privilege for high-risk accounts.
It allows you to:
- Define access based on roles (administrator, operator, supervisor)
- Control who can access which systems and when
- Regularly review and adjust user privileges
- Detect and eliminate excessive rights or forgotten accounts
More importantly, privileged activity is not just controlled — it is monitored and recorded. This makes access decisions transparent and auditable.
How Axidian Access enables granular access control
For non-privileged users, Axidian Access (IAM) provides granular control over access policies.
With it, you can clearly define:
- Who has access
- What resources are accessible
- Under which conditions access is granted
Access can be configured based on user roles, responsibilities, and even geolocation. This aligns directly with RBI’s “need-based access” requirement and helps organizations build a consistent and scalable access model.
Monitoring and MFA for privileged users: RBI control #19 (b) and (c)
What RBI requires
RBI goes further than access control. Controls #19 (b) and (c) require:
- Continuous supervision of privileged users
- Logging and periodic review of their activities
- Mandatory MFA for privileged access
This means organizations must not only restrict access, but also track and verify how it is used.
How Axidian Privilege enforces control and visibility
Axidian Privilege is designed exactly for this purpose.
It allows organizations to:
- Monitor all privileged sessions in real time
- Record sessions (video, logs, screenshots)
- Maintain full audit trails of user activity
- Enforce least privilege dynamically
Another critical function is credential management. Privileged credentials are stored securely inside the system and are not exposed to users. This significantly reduces the risk of compromise and eliminates unsafe practices like password sharing.
Built-in MFA for privileged access
RBI also requires MFA for privileged users — and Axidian Privilege includes it out of the box.
It supports multiple authentication methods:
- One-time passwords (OTP)
- Push notifications
- Biometrics
- Hardware tokens
Importantly, MFA is a built-in part of Axidian Privilege — it does not require additional licenses or integrations. This simplifies implementation and reduces operational overhead.
Implementing MFA across systems: RBI control #20
What RBI expects from MFA
Control #20 extends MFA requirements beyond privileged users. It requires organizations to implement multi-factor authentication for critical systems and activities based on risk assessment.
In practice, this means MFA must be applied consistently across the IT environment — not just in isolated systems.
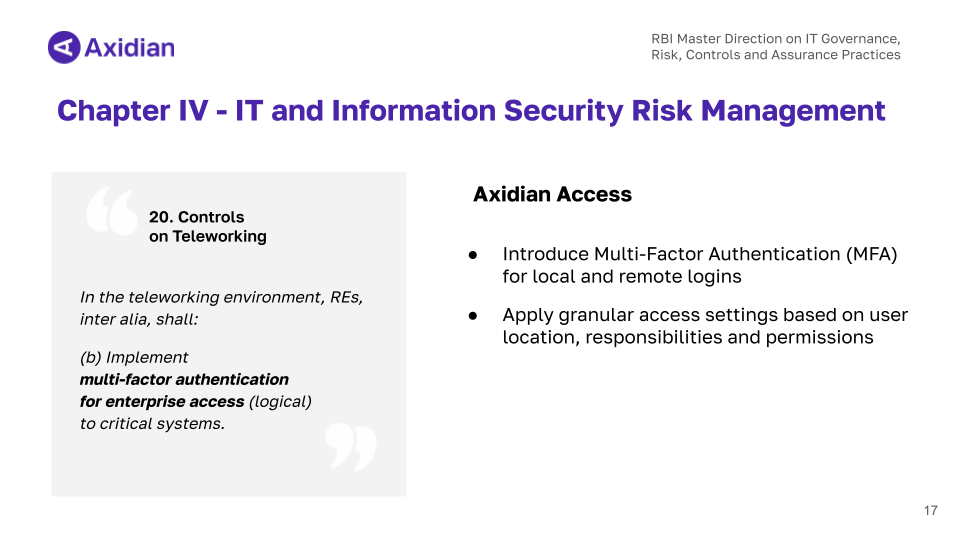
How Axidian Access delivers MFA and centralized control
Axidian Access provides centralized MFA and access management across the organization.
It enables:
- MFA for all target systems (applications, VPN, infrastructure)
- Flexible authentication scenarios based on risk
- A centralized access point to all corporate resources
It supports a wide range of authentication technologies, including OTP, push notifications, biometrics, smart cards, and tokens. These can be combined depending on the context and security requirements.
At the same time, all access is managed from a single platform. This reduces manual effort and ensures consistency across systems — a key factor for passing RBI audits.
Beyond mandatory controls: strengthening broader RBI requirements
While MFA and PAM are mandatory, RBI compliance goes beyond access control.
Axidian solutions also help strengthen other areas of the Master Direction, including:
- Risk assessment and mitigation
- Third-party access management
- Logging and audit trails
- Cyber incident prevention and investigation
These areas are covered across Chapters 2, 3, and 5. While they may not always require specific tools explicitly, having structured access control and monitoring significantly improves compliance readiness.
RBI compliance in practice: Axidian experience in India
RBI compliance is not theoretical — it is tested in real audits. This is where implementation quality becomes critical.
Axidian has already implemented PAM and IAM solutions in 10+ banks in India, helping them address key compliance challenges.
Typical results include:
- Successful audit preparation aligned with RBI requirements
- MFA and SSO implementation for administrators
- Automated password rotation
- Security and control over all privileged sessions (RDP, SSH, web, VPN, and more)
- Advanced monitoring and investigation tools (session recording, command control)
- Flexible reporting for audits
- Fast and predictable deployment
These projects show that compliance is achievable when requirements are translated into structured controls.
Where to start with RBI compliance
Trying to address all RBI requirements at once can quickly become overwhelming. A more practical approach is to start with the controls that have the highest impact.
In most cases, this means focusing on:
- Access control
- MFA implementation
- Privileged access management
These areas form the backbone of RBI cybersecurity compliance. Once they are in place, it becomes much easier to address broader requirements.
Watch the webinar and get the RBI compliance guide
If you want to go deeper into RBI compliance and see the full step-by-step approach, we recommend watching the webinar and downloading the guide.
It includes:
- Structured checklists
- Practical explanations of RBI requirements
- A clear framework for audit preparation
Watch the webinar and download the guide using the button below.



