On February 18, Axidian hosted a webinar for Indian cybersecurity specialists “How to comply with RBI Master Direction on Cybersecurity.” The session was led by Kirill Bondarenko, Regional Director, and Olesya Druzhinina, Head of Business Development. The objective was practical: to outline a structured and audit-ready methodology for complying with RBI cybersecurity requirements..
Rather than reiterating regulatory language, the discussion centered on practical interpretation, supervisory expectations, and effective preparation strategies. Our aim was to reduce uncertainty and provide participants with a clear, actionable framework. Below are the key insights from the session.
RBI Master Directions
For decades, the Reserve Bank of India issued thousands of circulars, acts, and instructions. Since 2016, the regulator has been consolidating them into Master Directions to create a more structured regulatory framework. As a result, institutions now rely on consolidated documents rather than fragmented guidance.
The primary framework governing IT and cybersecurity obligations today is the Master Direction on Information Technology Governance, Risk, Controls and Assurance Practices, effective since November 7, 2023. With its introduction, previous circulars on the same topic were repealed. This makes the Master Direction the central reference point for RBI’s requirements on cybersecurity.
Why RBI compliance is not checklistable
We have structured our guidance into practical checklists to simplify preparation and bring order to the process. However, it is important to understand that checklists alone do not guarantee compliance. They are a foundation, not a substitute for supervisory judgment.
The reason is structural. RBI supervision is risk-based, dynamic, and partly confidential. Auditors often rely on previous inspection findings and assess how effectively earlier weaknesses were remediated.
Moreover, the Master Direction frequently uses terms such as “appropriately secured” or “appropriately trained.” These phrases are intentionally flexible. What is appropriate depends on the institution’s size, risk profile, operational complexity, and maturity level. Ultimately, the supervisor defines the depth and scope of the audit.
A structured approach to audit preparation
While compliance cannot be approached as a purely checklist-driven exercise, preparation can and should follow a structured methodology. During the session, Axidian presented a framework built around three pillars: documentation, technology controls, and recurring governance activities. Together, they create a clear and measurable compliance baseline.
To make this practical, we translated the Master Direction into structured checklists. The documentation checklist includes 37 specific items derived from explicit and implied regulatory requirements. These cover policies, procedures, risk management artifacts, governance approvals, and reporting mechanisms that institutions are expected to maintain and periodically review.
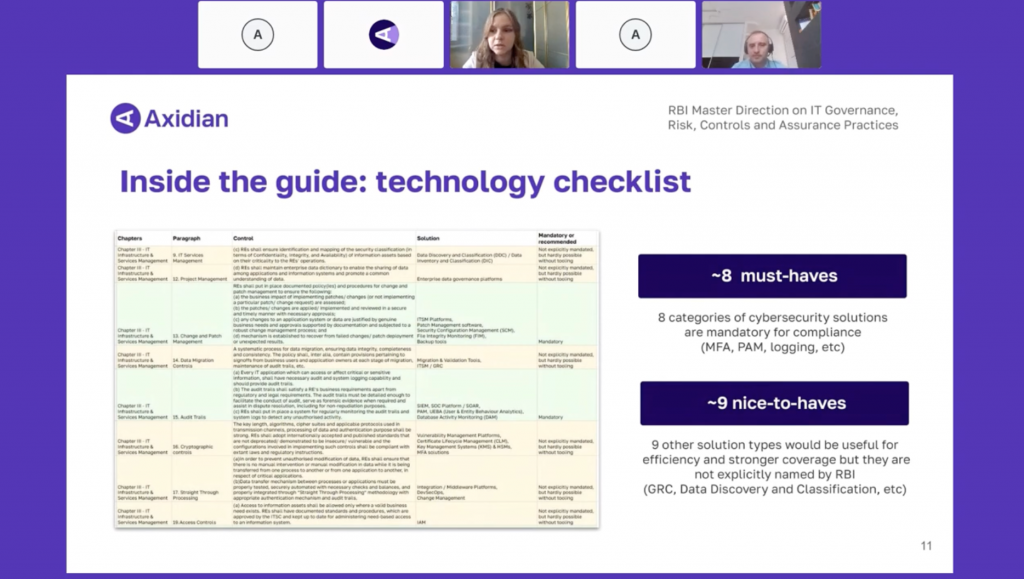
The technology checklist consolidates 19 categories of cybersecurity solutions, separating what is mandatory from what is not explicitly required but significantly simplifies compliance. This includes core controls such as MFA, centralized access management, logging, monitoring, and privileged access oversight. The objective is to help teams clearly distinguish between non-negotiable controls and architecture improvements that increase audit resilience.
Finally, we structured recurring obligations into a 19-point operational checklist, which effectively functions as a cybersecurity calendar. It consolidates all regular reviews, assessments, penetration tests, governance activities, and reporting cycles mentioned or implied in the Master Direction. This transforms compliance from a reactive audit preparation effort into an ongoing, predictable process.
This approach does not replace supervisory judgment. However, it significantly reduces stress and uncertainty during inspections. More importantly, it demonstrates operational discipline and order.
From regulatory requirements to structured implementation
Axidian works closely with cybersecurity specialists operating in regulated markets. Our focus is not limited to deploying security tools, but on helping teams build structured, auditable access control and governance processes.
If you missed the webinar on February 18, you can access the recording and download the compliance guide and structured checklists that we shared with attendees — by clicking the button below.



